Driving your FinOps strategy with observability best practices
Dynatrace
MARCH 18, 2024
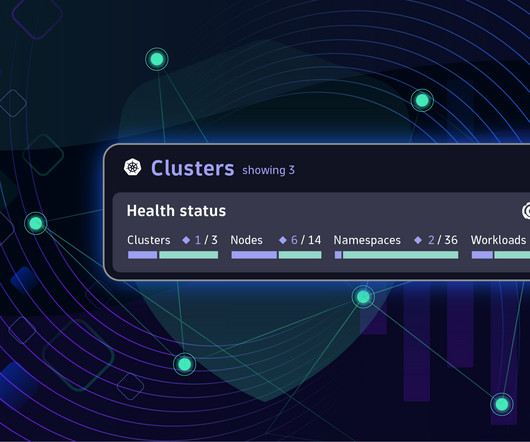
Empowering teams to manage their FinOps practices, however, requires teams to have access to reliable multicloud monitoring and analysis data. It’s about ensuring the cloud and IT resources you have provisioned are used completely and that your applications, transactions, and processes are using only necessary cloud computing resources.








































Let's personalize your content