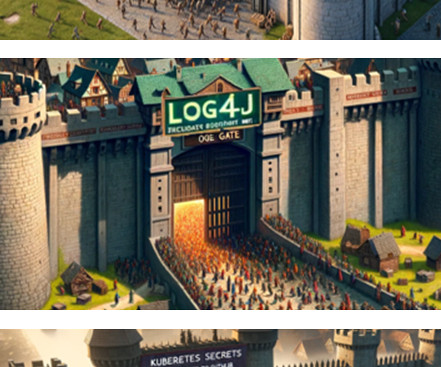
What is Log4Shell? The Log4Shell vulnerability explained (and what to do about it)
Dynatrace
DECEMBER 16, 2021
Because the Log4j 2 library can communicate with other sources and internal directory services, attackers can easily feed Log4j 2 with malicious commands from the outside and make it download and execute dangerous code from malicious sources. How Log4j 2 can be exploited depends on the specifics of the affected system.























Let's personalize your content