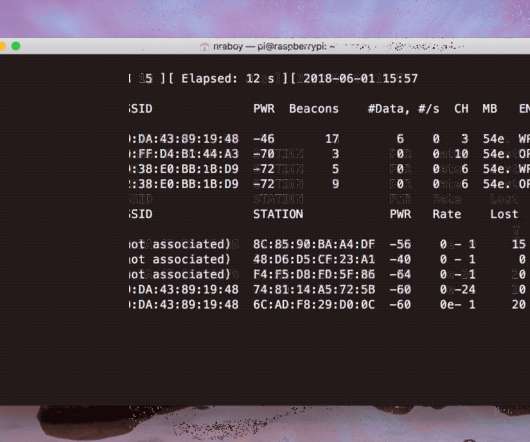
Crack Wireless Passwords Using A Raspberry Pi And Aircrack
The Polyglot Developer
JUNE 6, 2018
We wanted to explore some cybersecurity topics rather than programming which led us to network security. We decided to try to obtain the password to my wireless network password using the popular Aircrack-ng software. While it didn’t find my password in the end, it doesn’t mean we weren’t successful.













Let's personalize your content