50 ways to leak your data: an exploration of apps’ circumvention of the Android permissions system
The Morning Paper
SEPTEMBER 24, 2019
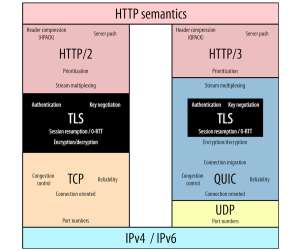
you should definitely check it out if you don’t already know it!). Network traffic is also monitored, included all TLS-secured traffic where the developers hadn’t used certificate pinning (i.e., Once the app has run in the rig for a while, the network traffic generated by the app is inspected to uncover leaked information.














Let's personalize your content