How low-code/no-code AutomationEngine advances automated workflows
Dynatrace
FEBRUARY 15, 2023
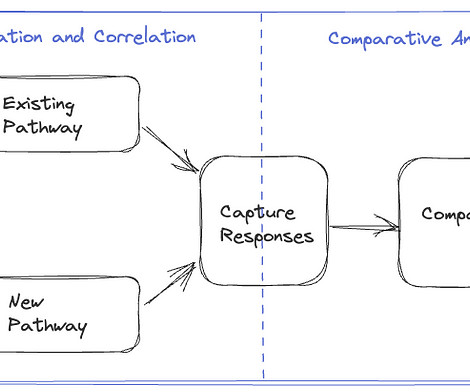
But to be scalable, they also need low-code/no-code solutions that don’t require a lot of spin-up or engineering expertise. With the Dynatrace modern observability platform, teams can now use intuitive, low-code/no-code toolsets and causal AI to extend answer-driven automation for business, development and security workflows.

































Let's personalize your content