Native App Network Performance Analysis
DZone
APRIL 7, 2021
When 54 percent of the internet traffic share is accounted for by Mobile , it's certainly nontrivial to acknowledge how your app can make a difference to that of the competitor!
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
DZone
APRIL 7, 2021
When 54 percent of the internet traffic share is accounted for by Mobile , it's certainly nontrivial to acknowledge how your app can make a difference to that of the competitor!
The Netflix TechBlog
NOVEMBER 17, 2022
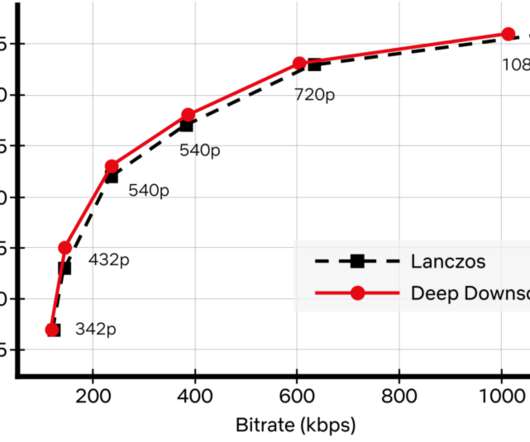
Recently, we added another powerful tool to our arsenal: neural networks for video downscaling. In this tech blog, we describe how we improved Netflix video quality with neural networks, the challenges we faced and what lies ahead. How can neural networks fit into Netflix video encoding?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Dynatrace
MARCH 27, 2024
By using AIOps to monitor events system-wide, teams can automate an array of common security processes, including application monitoring, threat intelligence analysis, and security incident response. This blog originally appeared in Federal News Network. When we protect our systems, we’re also protecting them.

Dynatrace
MAY 19, 2023
For cloud operations teams, network performance monitoring is central in ensuring application and infrastructure performance. If the network is sluggish, an application may also be slow, frustrating users. Worse, a malicious attacker may gain access to the network, compromising sensitive application data.
The Netflix TechBlog
JUNE 7, 2021
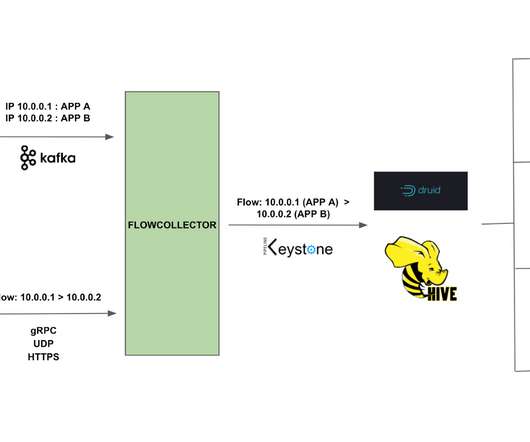
By Alok Tiagi , Hariharan Ananthakrishnan , Ivan Porto Carrero and Keerti Lakshminarayan Netflix has developed a network observability sidecar called Flow Exporter that uses eBPF tracepoints to capture TCP flows at near real time. Without having network visibility, it’s difficult to improve our reliability, security and capacity posture.

Dynatrace
NOVEMBER 24, 2021
Quick and easy network infrastructure monitoring. Quick and easy network infrastructure monitoring. Begin network monitoring by simply deploying an extension with just a few clicks. Simplified data analysis presented in topological context. Tired of constantly switching between all your monitoring tools? Pool nodes.

Dynatrace
AUGUST 10, 2021
Instantaneous crash analysis. This makes crash analysis pages so responsive that they’re nearly instantaneous—no waiting involved. That’s why we also improved the information density of the crash analysis pages. The post Faster crash analysis for mobile apps appeared first on Dynatrace blog. See all the details.

Dynatrace
FEBRUARY 9, 2023
Luckily, Dynatrace provides in-depth memory allocation monitoring, which allows fine-grained allocation analysis and can even point to the root cause of a problem. While memory allocation analysis can show wasteful or inefficient code, it can also reveal different problems, one of which we’ll examine in this blog post.

Dynatrace
NOVEMBER 30, 2022
Monitoring modern IT infrastructure is difficult, sometimes impossible, without advanced network monitoring tools. While the market is saturated with many Network Administrator support solutions, Dynatrace can help you analyze the impact on your organization in an automated manner. Sample SNMP-enabled device configuration. What’s next?

Dynatrace
SEPTEMBER 22, 2021
network connectivity). Session details provide valuable information about the actual device, active app version, network connection and more …. User actions show exact timing of user interactions with drill-down options to network requests or crashes. 2: Details about every action taken until the crash.

Dynatrace
OCTOBER 4, 2022
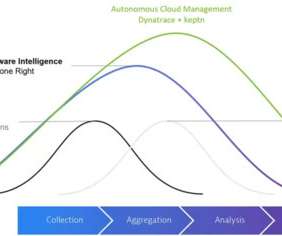
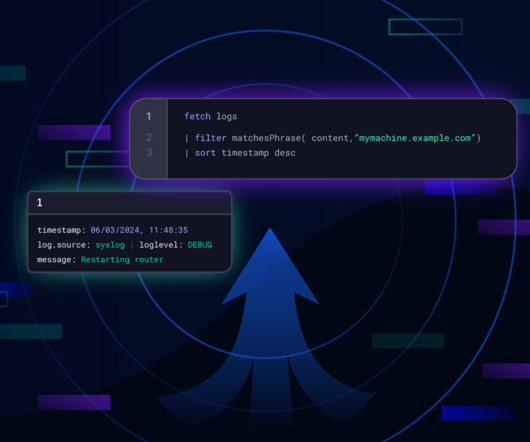
The number and variety of applications, network devices, serverless functions, and ephemeral containers grows continuously. Still, it is critical to collect, store, and make easily accessible these massive amounts of log data for analysis. Current analytics tools are fragmented and lack context for meaningful analysis.
Dynatrace
JULY 31, 2020
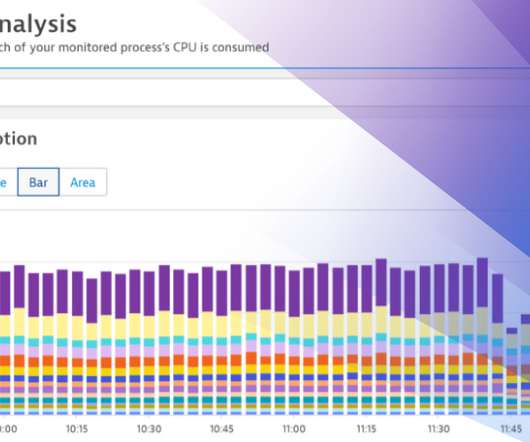
We’re happy to announce that with Dynatrace version 1.198, we’ve dramatically improved CPU analysis, allowing you to easily understand CPU consumption over time, in the context of your workloads. All deeper analysis actions are performed across the entire timeframe. Easily identify and analyze your most impacting workloads.

DZone
APRIL 19, 2019
Network monitoring, at scale, is an age-old problem in IT. In this post, I’ll discuss a brief history of network monitoring tools — including the pain points of legacy technology when it came to monitoring thousands of devices — and share my modern-day solution using Sensu Go and Ansible.
The Netflix TechBlog
APRIL 20, 2020
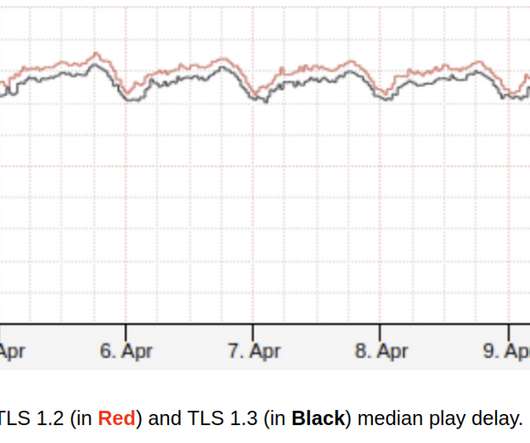
How Netflix brings safer and faster streaming experience to the living room on crowded networks using TLS 1.3 We want playback to start instantly and to never stop unexpectedly in any network environment. Therefore, it requires more messages to perform a handshake and two network round trips. Reduced Handshake TLS 1.2

Percona
JULY 20, 2023
We often forget or take for granted the network hops involved and the additional overhead it creates on the overall performance. TCP/IP connection, triggered me to write about other aspects of network impact on performance. How to detect and measure the impact There is no easy mechanism for measuring the impact of network overhead.

Dynatrace
JUNE 17, 2019
Juniper Network devices help enterprises connect and secure their applications, data, and services. Juniper Network devices utilizing Junos OS 7.4. Monitoring Juniper Network devices with Dynatrace is about to get even better. The post Juniper Networks ActiveGate extension now available (EAP) appeared first on Dynatrace blog.

Dynatrace
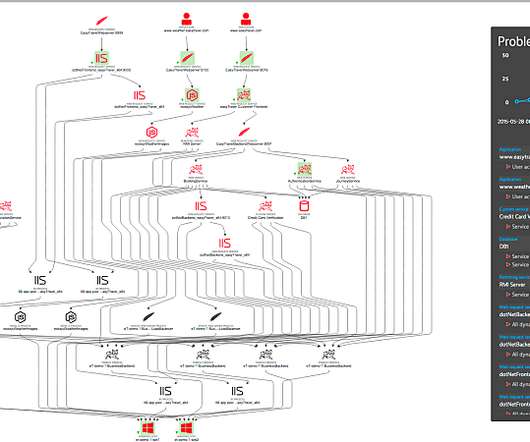
JULY 24, 2023
Unlike correlation-based machine learning, which calculates probabilities based on statistics, causal AI uses fault-tree analysis to determine system-level failures based on component-level failures. Causal AI draws on supporting data, such as relationships, dependencies, and other context among network entities and events.

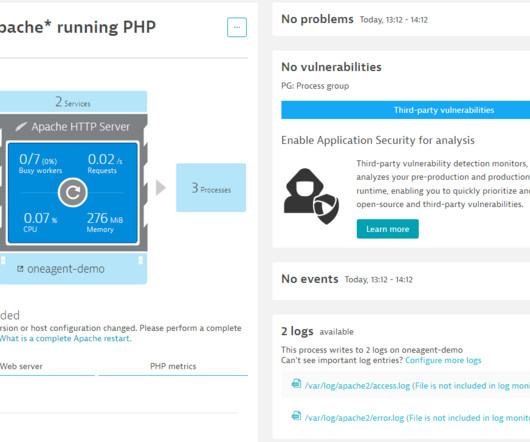
Dynatrace
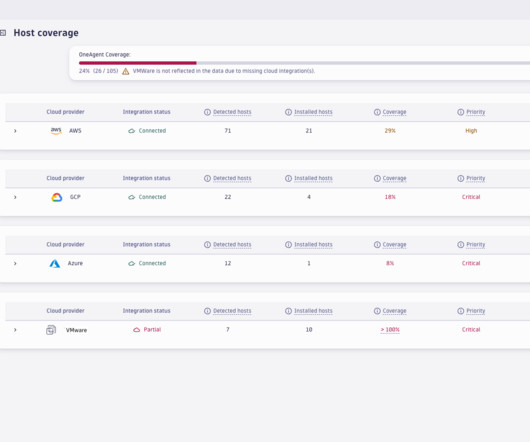
FEBRUARY 1, 2024
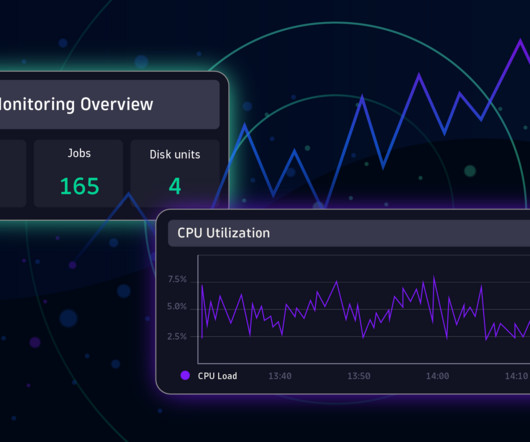
Immediately, you can spot and understand issues with problematic hosts and seamlessly organize them according to vital health metrics, such as CPU load, available memory, disk capacity, and network connectivity, facilitating prompt and efficient issue resolution. The process analysis page enables you to quickly identify problematic processes.
Dynatrace
OCTOBER 23, 2023
Firstly, managing virtual networks can be complex as networking in a virtual environment differs significantly from traditional networking. This leads to a more efficient and streamlined experience for users. Challenges with running Hyper-V Working with Hyper-V can come with several challenges.
Dynatrace
APRIL 3, 2024
A security operations center plays a crucial role in protecting a state agency by focusing on threat detection, analysis, and response. This includes not only infrastructure connections but also the relationships and dependencies between containers, microservices , and code at all network layers. What is a security operations center?

DZone
DECEMBER 19, 2020
BPF is mainly used for networking, tracing, and security. A practical solution is Berkeley Packet Filter (BPF), a highly flexible, efficient virtual machine that runs in the Linux kernel. It allows bytecode to be safely executed in various hooks, which exist in a variety of Linux kernel subsystems.
Dynatrace
MARCH 6, 2024
The entire topology is built on Dynatrace based on the components it finds configured on your IBM i system, all acting cohesively to accelerate root cause and impact analysis. Nothing is installed on your IBM i systems. It’s all monitored remotely !

Dynatrace
NOVEMBER 6, 2023
But there’s more than just a need for minimizing resource (CPU, memory, storage) and network (bandwidth) consumption for observability at the edge. Moreover, edge environments can be highly dynamic, with devices frequently joining and leaving the network.

Dynatrace
MARCH 18, 2024
OpenTelemetry standardizes how organizations instrument, generate, and collect telemetry data for analysis and provides community-based support. Users can run the Dynatrace OTel Collector to mask sensitive data next to applications and ensure that no sensitive data leaves the internal network. Ingest and multiplex data.

Dynatrace
JULY 25, 2022
This new service enhances the user visibility of network details with direct delivery of Flow Logs for Transit Gateway to your desired endpoint via Amazon Simple Storage Service (S3) bucket or Amazon CloudWatch Logs. AWS Transit Gateway is a service offering from Amazon Web Services that connects network resources via a centralized hub.

Dynatrace
JUNE 6, 2023
Comprehensive platform solutions that provide full-stack monitoring with AI at their core can automatically detect anomalies and provide root-cause analysis to prevent future issues. Networking. Large-scale, multicloud deployments can introduce challenges related to network visibility and interoperability. AI-powered analytics.

Dynatrace
MARCH 22, 2021
As a Network Engineer, you need to ensure the operational functionality, availability, efficiency, backup/recovery, and security of your company’s network. Moreover, with the new metric browser , you can easily list and filter available metrics, chart metrics, and view automated multidimensional analysis. Events and alerts.
Dynatrace
DECEMBER 15, 2022
Besides the traditional system hardware, storage, routers, and software, ITOps also includes virtual components of the network and cloud infrastructure. A network administrator sets up a network, manages virtual private networks (VPNs), creates and authorizes user profiles, allows secure access, and identifies and solves network issues.
Dynatrace
FEBRUARY 28, 2024
Exploratory data analytics is an analysis method that uses visualizations, including graphs and charts, to help IT teams investigate emerging data trends and circumvent issues, such as unexpected traffic spikes or performance degradations.
DZone
JANUARY 31, 2024
Key Components in SIEM Log Collection: SEIM systems collect and aggregate log data from Various sources across an organization’s network, including servers, endpoints, firewalls, applications, and other devices. For example, in big organizations, the Linux logs may be around 10 billion, and firewall logs may be around five billion per day.
Dynatrace
JANUARY 31, 2024
Davis provides automatic anomaly detection and root-cause analysis, precisely pinpointing performance and security issues and enabling the automatic generation of detailed tickets with automatic routing to the appropriate team. Infrastructure monitoring mode offers the same capabilities except tracing and profiling.

Dynatrace
SEPTEMBER 7, 2022
VPC Flow Logs is an Amazon service that enables IT pros to capture information about the IP traffic that traverses network interfaces in a virtual private cloud, or VPC. By default, each record captures a network internet protocol (IP), a destination, and the source of the traffic flow that occurs within your environment.
Dynatrace
JANUARY 31, 2024
Troubleshoot faster with quick, automated root-cause analysis within SAP and between SAP and non-SAP integrated domains. This approach enables unified analysis and troubleshooting of the complete IT stack, from infrastructure through non-SAP systems to SAP-focused monitoring, all in a single AI-powered observability platform—Dynatrace.

Dynatrace
MARCH 20, 2024
Continuously monitoring application behavior, network traffic, and system logs allows teams to identify abnormal or suspicious activities that could indicate a security breach. Forensics focuses on the systemic investigation and analysis of digital evidence to determine root causes.
Dynatrace
NOVEMBER 1, 2022
These metrics help to keep a network system up and running?, A 2022 Outage Analysis report found that enterprises are struggling to achieve a measurable reduction in outage rates and severity. Maintenance: Reduces the risk of an incident occurring again with root-cause analysis and continuous improvements to the system.

Dynatrace
DECEMBER 13, 2023
Mobile applications (apps) are an increasingly important channel for reaching customers, but the distributed nature of mobile app platforms and delivery networks can cause performance problems that leave users frustrated, or worse, turning to competitors. Load time and network latency metrics. Minimize network requests.
Dynatrace
MARCH 15, 2024
Getting insights into the health and disruptions of your networking or infrastructure is fundamental to enterprise observability. For example, a supported syslog component must support the masking of sensitive data at capture to avoid transmitting personally identifiable information or other confidential data over the network.

Dynatrace
MARCH 13, 2024
The Network and Information Systems 2 (NIS2) Directive, which goes into effect in Oct 2024, aims to enhance the security of network and information systems throughout the EU. NIS2 is an evolution of the Network and Information Systems (NIS) Security Directive, which has been in effect since 2016.

Dynatrace
OCTOBER 13, 2021
Examples of such weaknesses are errors in application code, misconfigured network devices, and overly permissive access controls in a database. In all, there are seven types of vulnerability assessments, each with its own focus and methods: Application analysis has two types: static and dynamic. Analyze findings.

Dynatrace
NOVEMBER 15, 2021
Log monitoring, log analysis, and log analytics are more important than ever as organizations adopt more cloud-native technologies, containers, and microservices-based architectures. A log is a detailed, timestamped record of an event generated by an operating system, computing environment, application, server, or network device.

Dynatrace
MAY 31, 2023
Uptime Institute’s 2022 Outage Analysis report found that over 60% of system outages resulted in at least $100,000 in total losses, up from 39% in 2019. The growing amount of data processed at the network edge, where failures are more difficult to prevent, magnifies complexity.
Dynatrace
MAY 17, 2023
This allows us to quickly tell whether the network link may be saturated or the processor is running at its limit. The other sections on that page (such as Disk analysis) provide further information and charts on topics such as available disk space, latency, dropped network packets, refused connections, and more.

Dynatrace
SEPTEMBER 8, 2022
Log management is an organization’s rules and policies for managing and enabling the creation, transmission, analysis, storage, and other tasks related to IT systems’ and applications’ log data. Log monitoring enables the collection of log data, and log analysis promotes intelligent, data-driven decision making. Dynatrace news.

Dynatrace
JULY 25, 2023
Davis AI transforms and augments data to enable more useful analysis, perform automatic tasks, and respond to user requests: Predictive AI uses machine learning (ML) and statistical methods to recommend future actions based on data from the past. When a user asks a question, generative AIs create an answer word by word.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content