50 ways to leak your data: an exploration of apps’ circumvention of the Android permissions system
The Morning Paper
SEPTEMBER 24, 2019
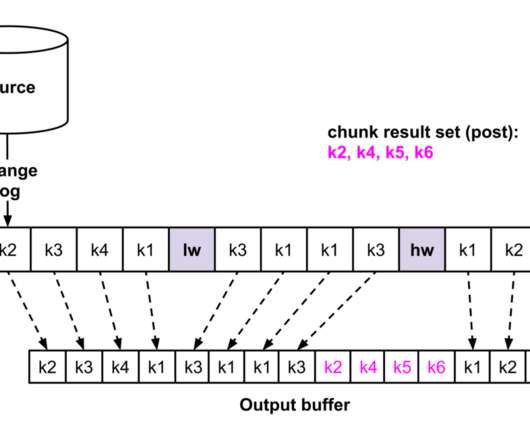
USENIX Security Symposium 2019. Network traffic is also monitored, included all TLS-secured traffic where the developers hadn’t used certificate pinning (i.e., Once the app has run in the rig for a while, the network traffic generated by the app is inspected to uncover leaked information. most apps).


















Let's personalize your content